实验目的:
1、掌握自反ACL的基本编写。
2、理解自反ACL的基本特性。
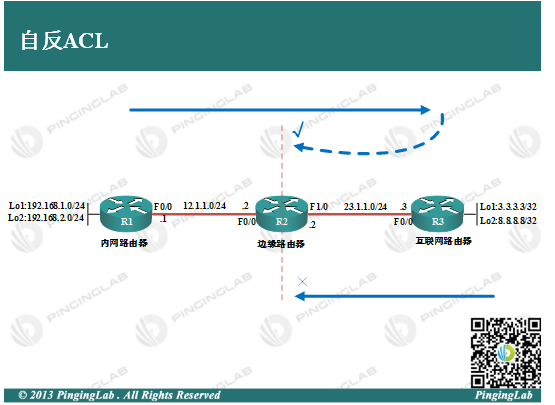
实验拓扑:
实验步骤:
1、依据图中拓扑,配置各个路由器的IP地址,并部署静态路由保证全网连通,配置如下:
R1上
R1(config)#ip route 23.1.1.0 255.255.255.0 12.1.1.2 R1(config)#ip route 3.3.3.3 255.255.255.255 12.1.1.2 R1(config)#ip route 8.8.8.8 255.255.255.255 12.1.1.2
R2上
R2(config)#ip route 192.168.1.0 255.255.255.0 12.1.1.1 R2(config)#ip route 192.168.2.0 255.255.255.0 12.1.1.1 R2(config)#ip route 3.3.3.3 255.255.255.255 23.1.1.3 R2(config)#ip route 8.8.8.8 255.255.255.255 23.1.1.3
R3上
R3(config)#ip route 12.1.1.0 255.255.255.0 23.1.1.2 R3(config)#ip route 192.168.1.0 255.255.255.0 23.1.1.2 R3(config)#ip route 192.168.2.0 255.255.255.0 23.1.1.2
测试连通性,如下:
R1#ping 3.3.3.3 source 192.168.1.1 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 3.3.3.3, timeout is 2 seconds: Packet sent with a source address of 192.168.1.1 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 40/40/40 ms R1#ping 8.8.8.8 source 192.168.2.1 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 8.8.8.8, timeout is 2 seconds: Packet sent with a source address of 192.168.2.1 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 36/43/56 ms
可以看到,内网与外网通信没有问题。
2、在R2上部署自反ACL,使得内网所有设备可以访问外网,而外网主动发起的流量都拒绝,配置如下:
①允许内网访问外网流量,并执行流量“记录”
R2(config)#ip access-list extended OUTBOUND R2(config-ext-nacl)#permit ip any any reflect PL R2(config-ext-nacl)#exit R2(config)#ip access-list extended INBOUND
②拒绝外网访问内网,除了被”记录“的流量
R2(config-ext-nacl)#evaluate PL R2(config-ext-nacl)#deny ip any any R2(config-ext-nacl)#EXIT
③接口下调用ACL
R2(config)#int f1/0 R2(config-if)#ip access-group OUTBOUND out R2(config-if)#ip access-group INBOUND in R2(config-if)#exit
3、测试自反ACL,如下:
在R2上查看ACL状态
R2#show ip access-lists
Extended IP access list INBOUND
10 evaluate PL
20 deny ip any any
Extended IP access list OUTBOUND
10 permit ip any any reflect PL
Reflexive IP access list PL
让R1访问外网
R1#ping 8.8.8.8 source 192.168.1.1 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 8.8.8.8, timeout is 2 seconds: Packet sent with a source address of 192.168.1.1 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 60/63/64 ms
再次在R2上查看ACL状态
R2#show ip access-lists
Extended IP access list INBOUND
10 evaluate PL
20 deny ip any any
Extended IP access list OUTBOUND
10 permit ip any any reflect PL (10 matches)
Reflexive IP access list PL
permit icmp host 8.8.8.8 host 192.168.1.1 (20 matches) (time left 298)
从上面可以看出,当内网访问外网时,由于实现了流量“记录”,自反ACL自动生成一条反向ACL,用于放开内网到外网的返回流量。而没有被记录的或者外网主动发起的流量,则被拒绝,如下:
R3#ping 192.168.1.1 source 3.3.3.3 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 192.168.1.1, timeout is 2 seconds: Packet sent with a source address of 3.3.3.3 UUUUU Success rate is 0 percent (0/5)
通过这个实验可以看到,自反ACL可以实现更加安全的访问控制,某种程度上可以充当防火墙。此实验完成。
- 还没有人评论,欢迎说说您的想法!
